The number of software security vulnerabilities continues to hit record highs, yet vulnerability analysis typically requires manual involvement and is extremely time-consuming. To pre-detect vulnerabilities in containers, it often involves retrieving, understanding, and consolidating hundreds of pieces of information. By leveraging generative AI and Retrieval-Augmented Generation (RAG) technology, enterprises can drastically reduce the time required to assess and mitigate risks from common vulnerabilities and exposures (CVEs)—from hours or days down to seconds—while maintaining high accuracy.
The Security Vulnerability Analysis AI Workflow demonstrates how to use NVIDIA NIM™ microservices and NVIDIA Morpheus to develop solutions that accelerate CVE risk analysis in software containers.
What Does This Workflow Include?
A reference solution that provides guidance for building event-driven RAG applications using NVIDIA NIM microservices, NeMo™ Retriever, and Morpheus.
An agent-based sense-reason-act loop that enables automated security checklist validation without manual intervention.
A large language model trained and fine-tuned on security documents, which can generate custom checklists.
Summaries for human decision-makers to help determine whether a container is ready for deployment.
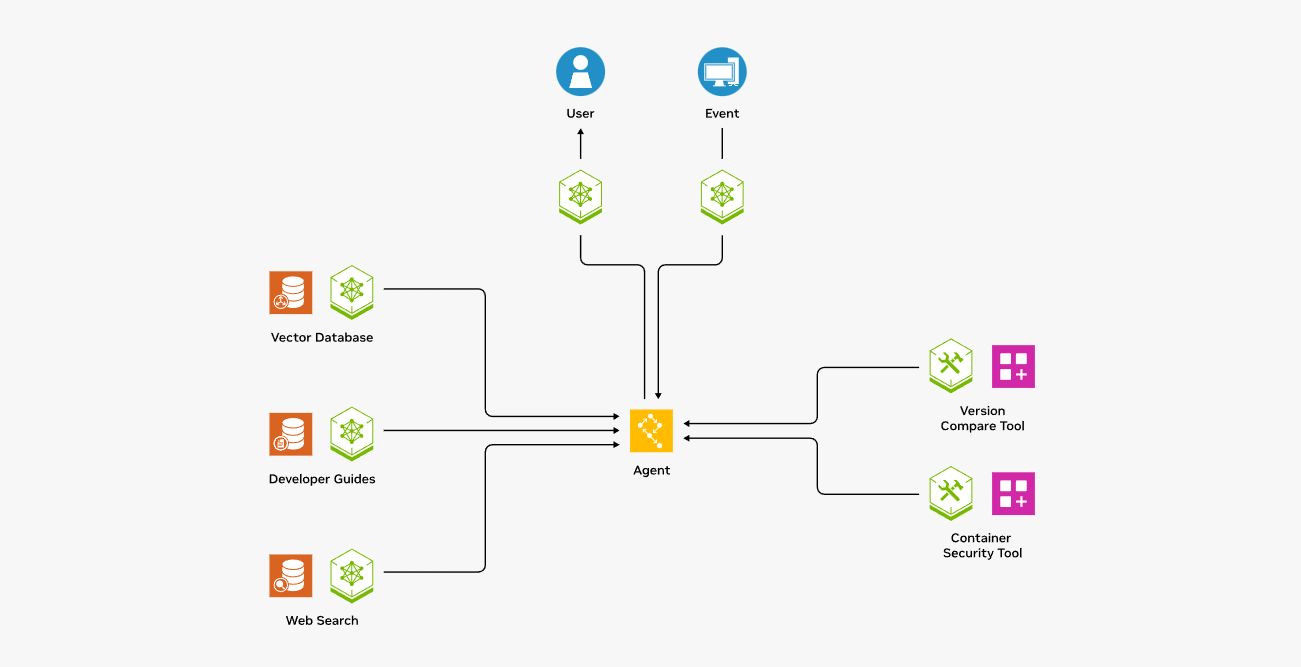
The LLM agent can periodically execute the sense-reason-act loop without human assistance: it runs checks based on checklists, then presents summarized results to human analysts—helping them make final decisions more quickly.